Remote Code Execution (RCE) vulnerability in Hikvision IP camera/NVR firmware (CVE-2021-36260)
Summary
The majority of the recent camera product ranges of Hikvision cameras are susceptible to a critical remote unauthenticated code execution vulnerability even with the latest firmware (as of 21 June 2021). Some older models are affected also as far back as at least 2016. Some NVRs are also affected, though this is less widespread.Hikvision’s security advisory: security-notification-command-injection-vulnerability-in-some-hikvision-products
This permits an attacker to gain full control of the device with an unrestricted root shell, which is far more access than even the owner of the device has as they are restricted to a limited “protected shell” (psh) which filters the input to a predefined set of limited, mostly informational commands.
In addition to complete compromise of the IP camera, internal networks can then be accessed and attacked.
A list of affected firmware types can be found at the end of this document.
Firmware from as long ago as 2016 has been tested and found to be vulnerable.
The only access to the HTTP(s) server port (typically 80/443) is needed. No username or password is needed nor do any actions need to be initiated by the camera owner. It will not be detectable by any logging on the camera itself.
This vulnerability was reported to Hikvision the day after the discovery, on 21 June 2021. I wrote a full report to them identifying the problem code, the device types affected, POC, and recommendations for resolution.
At the time of writing, patched firmware is partially available through inconsistently deployed across various Hikvision firmware portals.
Risk Assessment
Impact:
- Remotely Exploitable: Yes
- Authentication Required: None
- Zero clicks (no action needed from device owner): Yes
- Render device inoperable: Yes
- Read customer data: Yes
- Change customer data: Yes
- Latest firmware vulnerable: Yes (as of 21 June 2021)
- Latest products vulnerable: Yes
- Denial of Service vulnerability: Yes
- Potentially enable a physical attack on site: Yes
- Attack internal network: Yes
The is the most serious form of vulnerability for this device type.
Vulnerability Details
Not for public release to protect companies/end users.
Proof of Concept (POC) example
Hikvision HSRC (Hikvision Security Response Center) requested POC of the vulnerability when I first reported it to them, and I replied with working code within 2 hours or so. As it’s not responsible to disclose a POC, I instead decided to make a video showing it in action, though I have subsequently agreed with Hikvision not to release it.
Rather than just use my own equipment as a target, which could seem contrived, I enlisted the aid of a friend from the http://ipcamtalk.com forum, who kindly put up a real live camera with permission to exploit. I wasn’t told the access credentials but during the attack, it was clear it’s running 2021 firmware, and the camera was manufactured in January 2021.
The video showed a real-world example of me attacking this target, obtaining information that should be only available to the owner, obtaining a root shell accessible via SSH (even though SSH disabled in the web interface), and ultimately bypassing the camera admin web portal authentication.
A few stills from the real target POC video
I don’t know the root/admin password.We get device information we shouldn’t be able to get, the contents of /etc/passwd (the admin account password is always the same as the camera web portal admin password) and add our own system root account:
Recommendations made to Hikvision:-
I made several recommendations in my report to HSRC. I identified the flawed code that was the problem and indicated how I thought it best to remedy it. I don’t have access to their codebase repositories, but rather needed to decrypt firmware, and reverse engineer code yet I still found it. Issue new firmware as soon as possible and issue a public security advisory.
Remediation
Received patched IPC_G3 (V5.5.800 build 210628) and IPC H5 (V5.5.800 build 210628) firmware from HSRC for testing.Decrypted and reversed the code, in addition, to live to test on my own equipment and confirmed to HSRC that the patched firmware resolves the vulnerability.
Was further pleased to note this problem was fixed in the way I recommended.
Is this a Chinese Government-mandated Backdoor?
No, definitely NOT. You wouldn’t do it like this. And not all firmware types are affected.
AdditionalI’m a security researcher who used to look after servers, networks, and 1000s of people’s data in a former life, and the last few months knowing this exists on such a large scale has been worrying.Still, I needed to wait 90 days after reporting before making any responsible public disclosure, whilst providing assistance to them and encouraging patched firmware to be developed, tested, published and a public security advisory issued.
I’d recommend you do not expose any IoT device to the Internet no matter who it is made by - or in which country the device is made (including the USA, Europe, etc). Use a VPN for access if needed. Block outbound traffic too if at all possible - I also like to give these devices the wrong gateway (router) IP.
Thank you to Hikvision - particularly the Head of HSRC, his team, and R&D for working hard to fix this quickly. I sent them lots of emails and reports which they kindly liaised with me on.
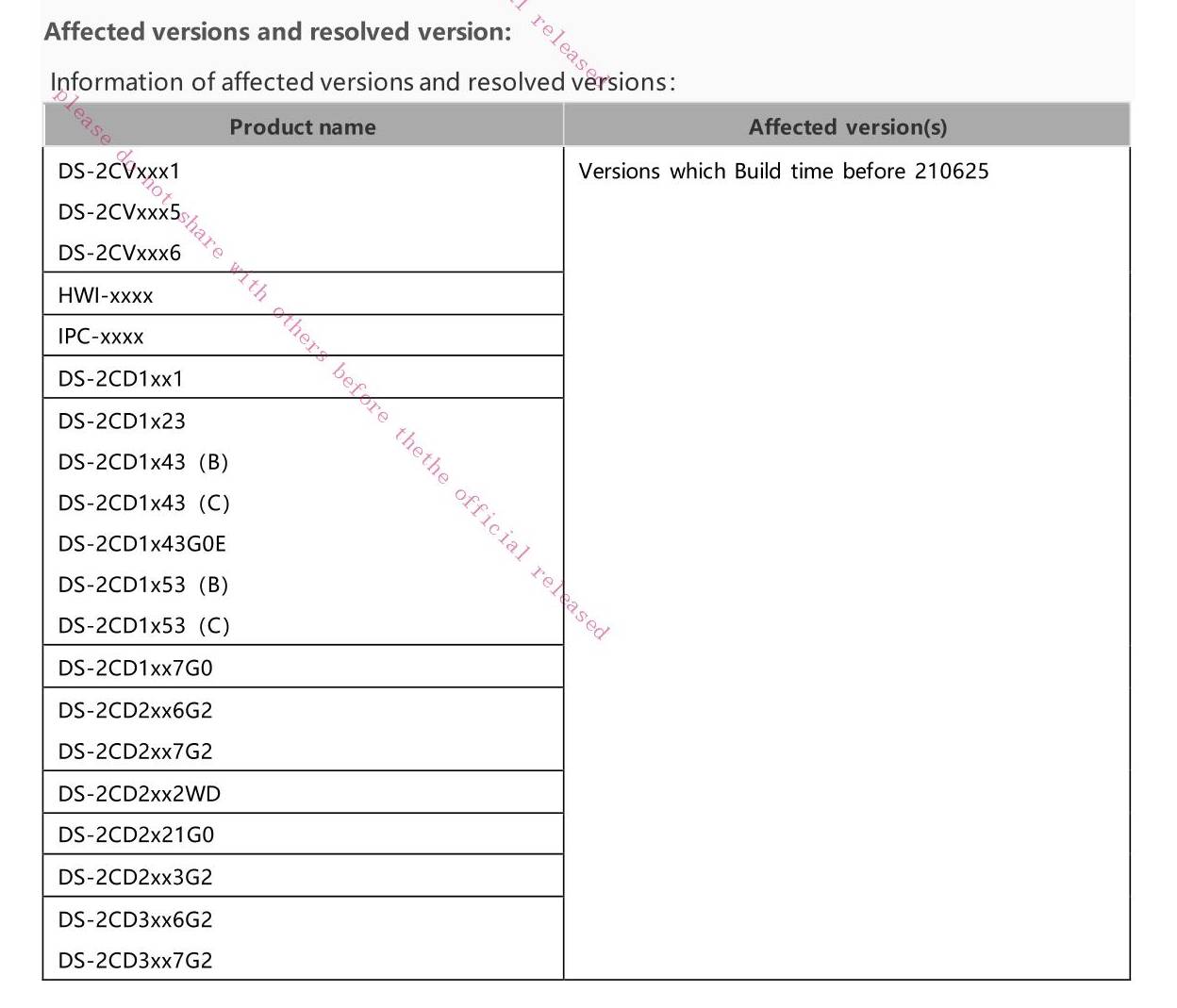
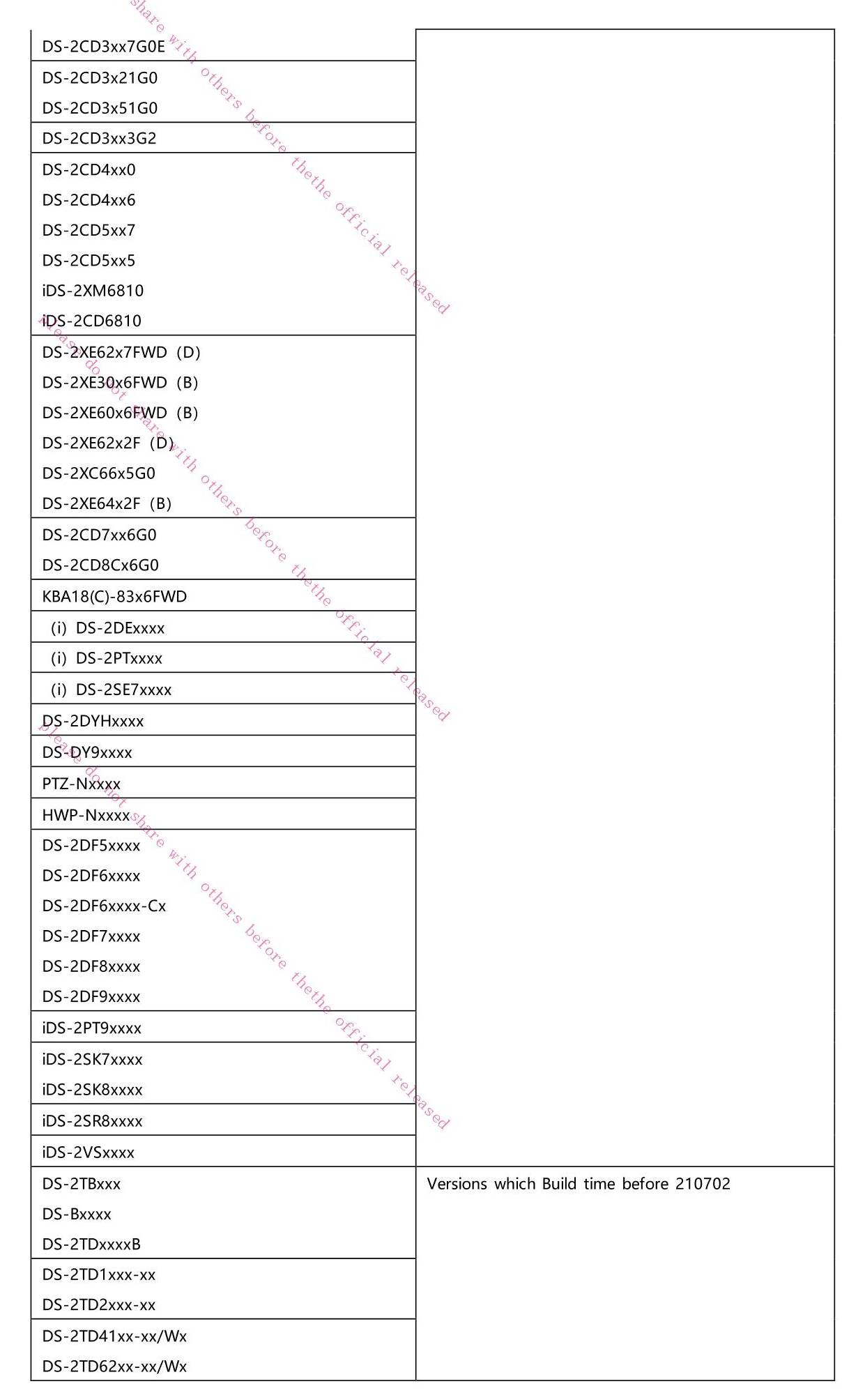
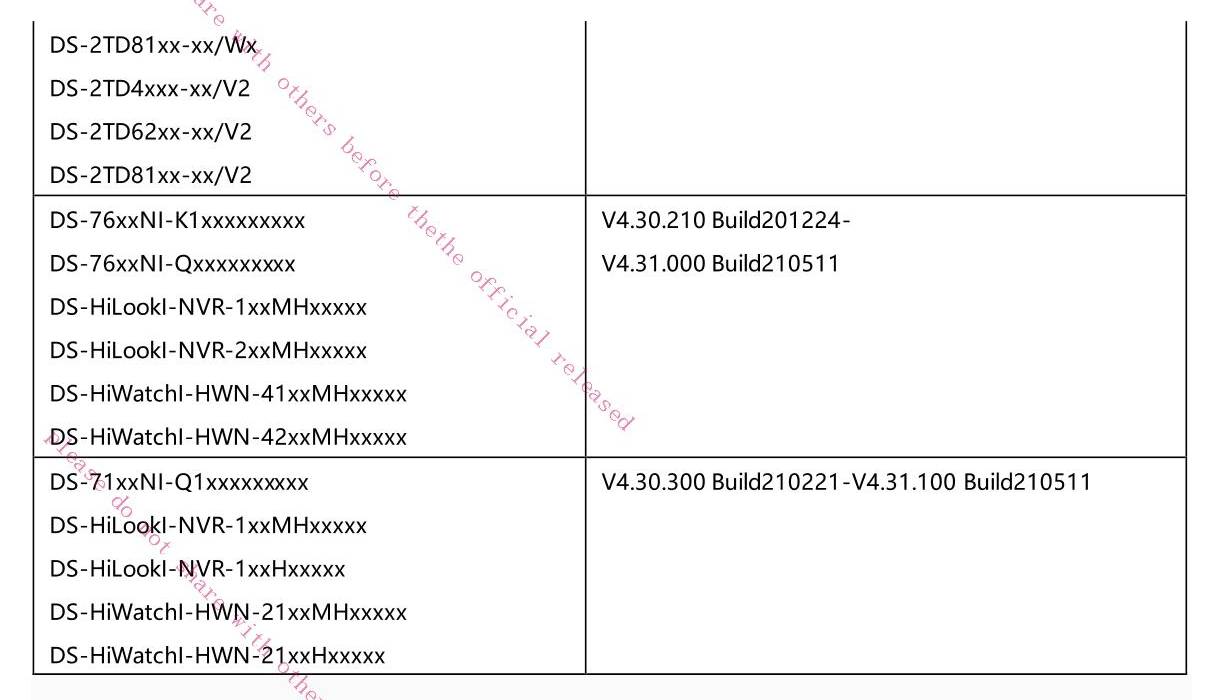
Affected Firmware Types
Notes:
I cannot decrypt all firmware types, nor access all versions so am unable to check all firmware.
Usually firmware types use the prefix IPC (IP Camera = not PTZ) or IPD (IP Dome = PTZ camera). Date code is in the form YYMMDD.
OEM firmware is not listed - there are too many to try to obtain and check.
At the time of writing updated firmware seems to be properly deployed on the Hikvision China region firmware portal for Chinese region devices, but only partially on the Global site. On the European www.hikvisioneurope.com and Russian http://ftp.hikvision.ru sites, even much of the updated firmware from the incomplete Global site is missing. Other regional portals are also likely unreliable.
Some NVRs are also affected, though they were not within the original scope of this report. Please refer to Hikvision’s advisory for more information.
Type Most recent vulnerable Firmware VersionIPC_E0 IPC_E0_CN_STD_5.4.6_180112
IPC_E1 unkown
IPC_E2 IPC_E2_EN_STD_5.5.52_180620
IPC_E4 unknown
IPC_E6 IPCK_H7_EN_STD_5.4.40_200226
IPC_E7 IPCK_E7_EN_STD_5.5.120_200604IPC_G3 IPC_G3_EN_STD_5.5.160_210416IPC_G5 IPC_G5_EN_STD_5.5.113_210317
IPC_H1 IPC_H1_EN_STD_5.4.61_181204
IPC_H5 IPCP_H5_EN_STD_5.5.85_201120
IPD_H8 Factory installed firmware mid 2021
IPC_R2 IPC_R2_EN_STD_V5.4.81_180203
Type Most recent vulnerable Firmware VersionIPC_E7 IPDEX_E7_EN_STD_5.6.30_210526IPD_G3 IPDEX_E7_EN_STD_5.5.42_210106IPC_H5 IPDEX_E7_EN_STD_5.5.41_200911IPC_H7 IPDEX_H7_EN_STD_5.4.40_200721IPD_H8 IPDEX_H8_EN_STD_5.7.1_210619
Type Vulnerable Firmware VersionIPC_R7 Up to 5.4.xIPD_R7 Up to 5.4.xIPC_GO Up to 5.4.xIPC_H3 Up to 5.4.xIPD_H3 Up to 5.4.x
Affected Model List
- Coming up with a proper affected model list is hard:
- Chinese region variants have often had their own model names.
- Some firmware does not have public release notes that list the compatible models
- There’s a huge number of OEM resellers with their own model numbers
For this reason, I think it better to simply include the list Hikvision have published in their security advisory:
Timeline
Manufacturer notified of issue: Monday 21 June 2021 16:16 to HSRC@hikvision.com and support.uk@hikvision.com. Unfortunately, HSRC didn’t receive this due to it being caught by a spam filter.
Wednesday 23 June 01:00 Follow up email to HSRC@hikvision.com and 400@hikvision.com, additionally sent a pdf copy of email via the vulnerability submission form at https://www.hikvision.com/europe/support/cybersecurity/report-an-issue/
- Wednesday 23 June 04:27 received a reply from HSRC@hikvision.com requesting a report on my findings.
- Wednesday 23 June 05:40 v1.0.0 of vulnerability details (WIP-2021-06-HIK-2) emailed to HSRC@hikvision.com
- Wednesday 23 June 2021 07:42 HSRC confirms they have reproduced the issue.
- Wednesday 07 July 2021 Request for disclosure timeline and CVE details in the next 7 days.
- Sunday 12 July 2021 HSRC inform me of the CVE ID they have applied for (CVE-2021-36260)
- Wednesday 04 August 2021 notify HSRC of my intention to make limited public disclosure 90 days after my initial report 20 September 2021. I insist companies/end-users know there is risk and they need to update devices.
- Tuesday 17 August 2021 HSRC send patched IPC_G3 (built 28 June 2021) and IPC_H5 (built 28 June 2021) for testing.
- Wednesday 18 August 2021 informed HSRC testing on patched firmware complete – urge them to release firmware as soon as possible on all firmware portals.
- Saturday 18 September 2021 Hikvision and I publish our respective advisory/report




Post a Comment